International Fraud Investigation Secrets Revealed: What Professional Scammers Don’t Want You to Know
Protect your assets. Uncover the truth. Secure your future. Scammers [...]
The Ultimate Guide to Legal Recovery for Romance Scams: Everything You Need to Succeed
Trust betrayed. Assets drained. Reality shattered. If you are reading [...]
Why Global Asset Tracing Will Change the Way You Handle Complex Legal Disputes
Find the money. Win the battle. Secure your future. You [...]
The Ultimate Guide to Fraud Investigation: Everything You Need to Succeed in Recovering Assets
Expert recovery. Proven results. Absolute discretion. Discovering you have been [...]
Why Comprehensive Commercial Insights Will Change the Way You Vet New Business Partners
Trust. Expertise. Results. You are about to sign a multi-year [...]
International Investigation Secrets Revealed: What Experts Don’t Want You to Know About Tracing Global Assets
Trust. Expertise. Results. You think your money is gone. You [...]
Your Investigation Data Won’t Hold Up in Court: How to Fix Your Evidence Trail Before Regulators Ask
Here's the uncomfortable truth: most companies collecting investigation data right now are building a house of cards. You think you're gathering evidence. What you're actually doing is creating a liability.
When the SFO, FCA, or SEC comes knocking: and they will: your beautifully documented investigation findings won't matter if the evidence itself can't survive legal scrutiny. One broken link in your chain of custody. One privacy law violation. One forensic misstep. That's all it takes to watch months of investigation work become inadmissible.
Let's fix that before regulators ask questions you can't answer.
Why Your Evidence Trail Is Already Compromised
You've launched an internal investigation. Your team has collected emails, extracted WhatsApp messages, pulled financial records from three different jurisdictions. Everything's saved on a shared drive. Job done, right?
Wrong. Catastrophically wrong.
Courts don't care about your good intentions. They care about one thing: can you prove this evidence is authentic, unaltered, and legally obtained? If you can't answer that question with documented certainty, your evidence is worthless.
The problems start immediately. Your IT team screenshots emails instead of preserving metadata. Your legal counsel downloads files to personal devices. Your investigator transfers data across borders without considering GDPR implications. Each action creates a vulnerability that opposing counsel will exploit.

The Chain of Custody Problem Nobody Talks About
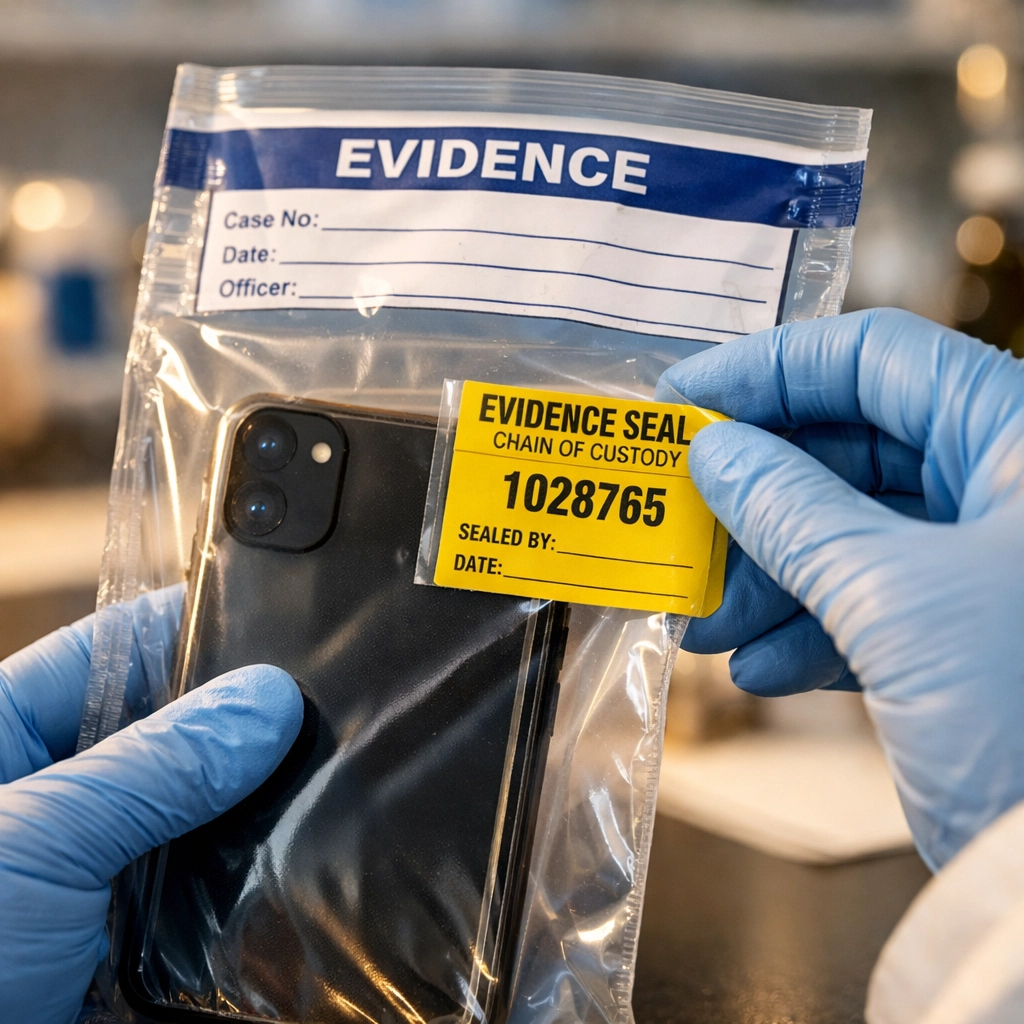
Chain of custody isn't just a box-ticking exercise. It's the foundational requirement that determines whether your evidence sees the inside of a courtroom or gets excluded before trial.
Here's what courts actually require: documented proof of every single person who touched that evidence, from collection to presentation. Every transfer. Every period of storage. Every moment of custody must be accounted for and recorded.
One gap? That's reasonable doubt.
The critical custody requirements you're probably missing:
- Identity verification – Can you prove who collected each piece of evidence and when?
- Continuity documentation – Do you have unbroken records showing where evidence was stored and who accessed it?
- Handling protocols – Did everyone who touched the evidence follow documented procedures?
- Access controls – Can you demonstrate that evidence was secured against tampering?
Without these elements, you don't have admissible evidence. You have expensive documents that won't survive a motion to exclude.
The fix starts with implementation of formal evidence handling protocols before collection begins. Every person involved in your investigation must understand their custody obligations. Every transfer must be logged. Every storage location must be secured and monitored.
Digital Forensics: Where Most Investigations Fail
Digital evidence is where amateur investigations collapse spectacularly. Your standard document collection methods destroy the very authenticity you need to prove in court.
Taking screenshots of emails? You've just eliminated metadata that proves when messages were actually sent and received. Copying files without forensic tools? You've altered creation dates and file properties. Accessing cloud storage without proper preservation? You've triggered data overwrites that defence counsel will argue constitute evidence spoliation.
Courts have strict standards for digital evidence. Evidence must be verified in terms of authenticity and integrity throughout collection, handling, testing, and storage procedures. Your casual approach to digital data won't meet that standard.
The forensic failures that sink cases:
- Metadata destruction – Copying or converting files without forensic imaging
- Device contamination – Powering on phones or computers without write-blocking
- Cloud data mishandling – Downloading rather than legally preserving cloud evidence
- Network data loss – Failing to preserve server logs and access records
- Mobile app evidence – Screenshots instead of forensically sound extractions
Professional digital forensics requires specialized tools and expertise. Forensic imaging creates exact replicas of devices while preserving all metadata. Write-blockers prevent contamination during examination. Chain of custody forms document every step.
You can't retrofit forensic standards after collection. Once evidence is compromised, it's compromised permanently.
Cross-Border Privacy Laws Will Destroy Your Evidence
Here's where it gets complicated: your investigation probably spans multiple jurisdictions. UK employees. EU servers. US cloud storage. Each jurisdiction has different privacy laws that govern how you can legally collect and transfer personal data.
Violate those laws, and your evidence becomes not just inadmissible: it becomes illegal.
GDPR imposes strict requirements on data collection, processing, and international transfers. The UK's Data Protection Act 2018 has similar protections. US state privacy laws add another layer of complexity. Collecting employee communications without proper legal basis? That's a GDPR violation. Transferring data from the EU to the US without adequate safeguards? Another violation. Processing more personal data than necessary for your investigation? Yet another violation.
Courts won't admit evidence obtained through privacy law violations. Worse, regulators can impose substantial fines for the violations themselves.
The cross-border pitfalls destroying evidence admissibility:
- Inadequate legal basis – Collecting data without legitimate grounds under applicable privacy law
- Excessive data collection – Gathering more information than necessary for investigation purposes
- Illegal international transfers – Moving data across borders without proper transfer mechanisms
- Consent failures – Relying on invalid consent when other legal bases are required
- Subject rights violations – Failing to honor data subject access or deletion requests during investigations

Navigating these requirements requires expertise across multiple jurisdictions. You need legal counsel who understands UK, EU, and US privacy frameworks simultaneously. You need documented processes that comply with the strictest applicable standard. You need to build privacy compliance into evidence collection from day one.
Act Before Regulators Force Your Hand
Here's the insider perspective: waiting until regulators request information is too late to fix your evidence problems.
When the SFO issues a Section 2 notice or the SEC opens a formal investigation, you have limited time to respond. If your evidence trail is compromised, you can't rebuild it under regulatory deadlines. You're stuck presenting flawed evidence or admitting you don't have admissible documentation.
Smart organizations build court-ready evidence collection processes before investigations begin. They establish forensic protocols. They implement chain of custody requirements. They ensure privacy law compliance across all jurisdictions where they operate.
This preparation serves two critical purposes. First, it ensures any internal investigation produces admissible evidence. Second, it demonstrates to regulators that your organization takes compliance seriously: a factor that influences enforcement decisions.
The proactive steps that protect you:
- Document evidence handling procedures before incidents occur
- Train investigation teams on chain of custody and forensic requirements
- Establish relationships with digital forensics experts who can respond immediately
- Create privacy-compliant data collection frameworks for each jurisdiction
- Implement secure evidence storage with access controls and audit trails
- Develop regulatory response plans that account for evidence admissibility requirements
Regulators evaluate your cooperation and compliance culture when deciding enforcement actions. Organizations with robust evidence handling demonstrate that culture. Organizations scrambling to collect admissible evidence after the fact don't.
How Zazinga Group Ensures Court-Ready Evidence
We've seen investigations collapse because evidence couldn't withstand scrutiny. We've watched organizations spend hundreds of thousands on investigations that produced inadmissible findings. We've fixed evidence trails that regulators initially rejected.
Our approach integrates legal expertise across UK, EU, and US jurisdictions with technical digital forensics capabilities. We don't just collect evidence: we build admissible evidence trails that survive court challenges.
When you engage our investigation services, we establish forensically sound collection protocols from the first day. We implement chain of custody documentation that courts require. We ensure privacy law compliance across every jurisdiction where evidence originates. We work with digital forensics experts who preserve metadata and authenticity.
The result: evidence that regulators accept and courts admit.
Your Evidence Trail Matters More Than Your Findings
You can conduct the most thorough investigation in your company's history. You can uncover fraud, misconduct, or compliance failures. You can document everything meticulously.
None of it matters if the evidence won't hold up in court.
Courts and regulators don't care about your conclusions. They care about admissible evidence that proves those conclusions. Chain of custody gaps, forensic failures, and privacy violations transform solid findings into inadmissible allegations.
The time to fix your evidence trail is now: before regulators ask to see it. Establish proper protocols. Implement forensic standards. Ensure privacy compliance. Document everything.
Or face the consequences when your investigation data can't survive legal scrutiny.
Contact us to ensure your investigation evidence meets court standards across UK, EU, and US jurisdictions. We build evidence trails that withstand regulatory and legal challenges( before you need them.)
